How Keycloak, as identity broker, simplifies the online world for companies and customers.
Keycloak in production as identity broker between different identity-managing systems.
Today, customers expect more convenience in e-commerce than a few years ago. Transactions via Internet portals are growing constantly and call for even more new, digital solutions.
Especially for a one-off purchase over the Internet, customers do not want to create another new account or assign a new password. Examples include the online purchase of a concert ticket or a travel ticket or to plan a shopping trip to the supermarket. With the Kaufland app, customers can decide whether they authenticate themselves with their customer account or via social networks. Even Deutsche Bank has recently started offering a login via the identity provider Verimi, if bank customers would like to log into their accounts. The use of an identity broker, which communicates with one or various identity providers, is worth it here in particular.
How does the technical implementation with Keycloak look?
We at the Login Alliance ask Hasebullah Ansari, because he is an expert in this field. He works with Syntlogo GmbH and has worked with Keycloak for more than three years. He completed his last project with Deutsche Bahn.
Login Alliance: “Mr Ansari, how does a company provide its applications as services in the Web via an identity broker?”
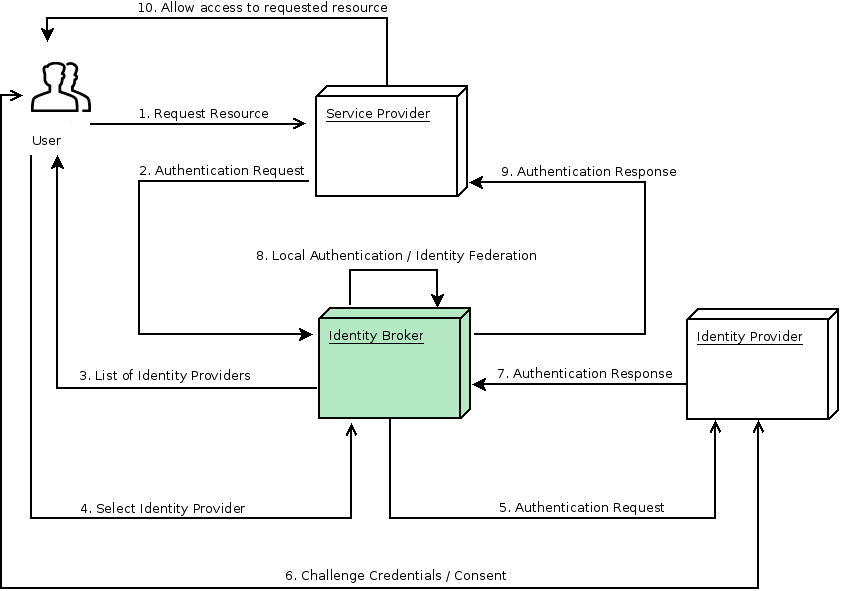
Hasebullah Ansari: “This is possible with Keycloak. The open source solution from Red Hat acts as an identity broker here between different identity providers. Keycloak references an account in a social media service (social networks like Facebook, Google, Twitter and the like), or alternatively a third party resource that supports OpenID Connect or SAML protocol.
This can be a purchased or self-developed application, but also an LDAP directory service, an Active Directory or the Kerberos authentication service. It is then called a user federation. Here, we are talking about a federated identity, since the identity information always remains with the respective, original resource. This has the great advantage that a user doesn’t have to create a new account for each, initial authentication.”
Login Alliance: “What possibilities are there if a user wants to access several applications of a company without having to enter passwords multiple times?”
Hasebullah Ansari: “The following options lend themselves to this.
- A Keycloak SSO implementation between different applications.
- Identity brokering (via OICD (OpenID Connect), SAML or an account with a social network).
- Or via a user federation (LDAP, Active Directory).”
Login Alliance: “Isn’t a system overwhelmed when very many users want to use an app at the same time?”
Hasebullah Ansari: “Naturally, in such a case, it is necessary to ensure high availability for the application and Keycloak (HA environment). You can use an HA cluster with multiple systems for this (master/slave cluster). There are two possibilities for a cluster setup in Keycloak: firstly a standalone HA cluster mode, and secondly the domain clustered mode.”
Our conclusion: Modern systems use Keycloak as an identity broker in order to save end customers from having to assign passwords once again or to create a new account. Existing accounts with Twitter, LinkedIn or Facebook can be used to make e-commerce services easy and convenient to use by means of Keycloak – an ideal solution!
Keycloak
Keycloak is an open source solution for identity and access management. It focuses on the protection of modern applications and services. With Keycloak you can safely implement the authentification to applications and services with less or no code.
Keycloak is functionally very extensive, user-friendly, and has an easy to use user interface, and it is multi-client capable.
What is an identity broker?
An identity broker is an intermediate service that connects multiple service providers with different identity providers. As an intermediary service, an identity broker is responsible for establishing a trust relationship with an external identity provider in order to use its identities to access internal services that are offered by service providers.
From the user’s perspective, an identity broker provides a user-orientated and centralised way to manage identities across different security domains or areas. It links an existing account with one or more identities of different identity providers, or even creates a new account on the basis of the identity information that it obtains from them.
An identity provider is usually based on a specific protocol. It is used for the authentication and communication of authentication and authorisation information to its users. It can be a social provider such as Facebook, Google or Twitter. It can be a business partner whose users would like to access your services. Or it is a cloud-based identity service that you would like to integrate.
Identity providers are usually based on the following protocols:
- SAML 2.0
- OAuth 2.0
- OpenID Connect
Learn more about Keycloak as an identity broker:
Go to the >>Server Administration Guide<<
(12. Identity Brokering) of Keycloak!